Setting Up Okta with Taplytics
This document is meant to provide an overview of how your team can set up Okta. It will also outline additional ways you can customize access to Taplytics for your team. It will be important to work closely with your CS Manager to enable the option that works best for your team and use case.
Okta Setup
Setup for Existing Taplytics Users
As the name suggests, this option allows users who already have existing Taplytics accounts to use Okta to access their team’s dashboard. This option will allow all logins via Okta.
Additional Options to Customize your Taplytics Access
Provision New Users into Taplytics
- These options will allow you to automatically provision users from specific domains (@gmail.com, @yourcompanyemail.com, etc) to specific Taplytics project environments with collaborator status when logging in for the first time using Okta
Exclusive Domain Login Methods
-
If you would like to only allow users to log in using specific methods, you may do this via this option. Specific login options include (Google SSO, password, Okta, etc)
-
This option will block all users from a specific domain (ex. @companydomain.com) from logging in using methods that aren't allowed
Invite Allow List
- This option allows you to limit the domains that are allowed to be sent invites via the taplytics project dashboard
Okta Login Setup, Start with the Below Two Steps
Please see the steps below for configuring Okta with Taplytics
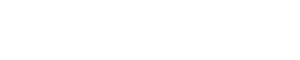
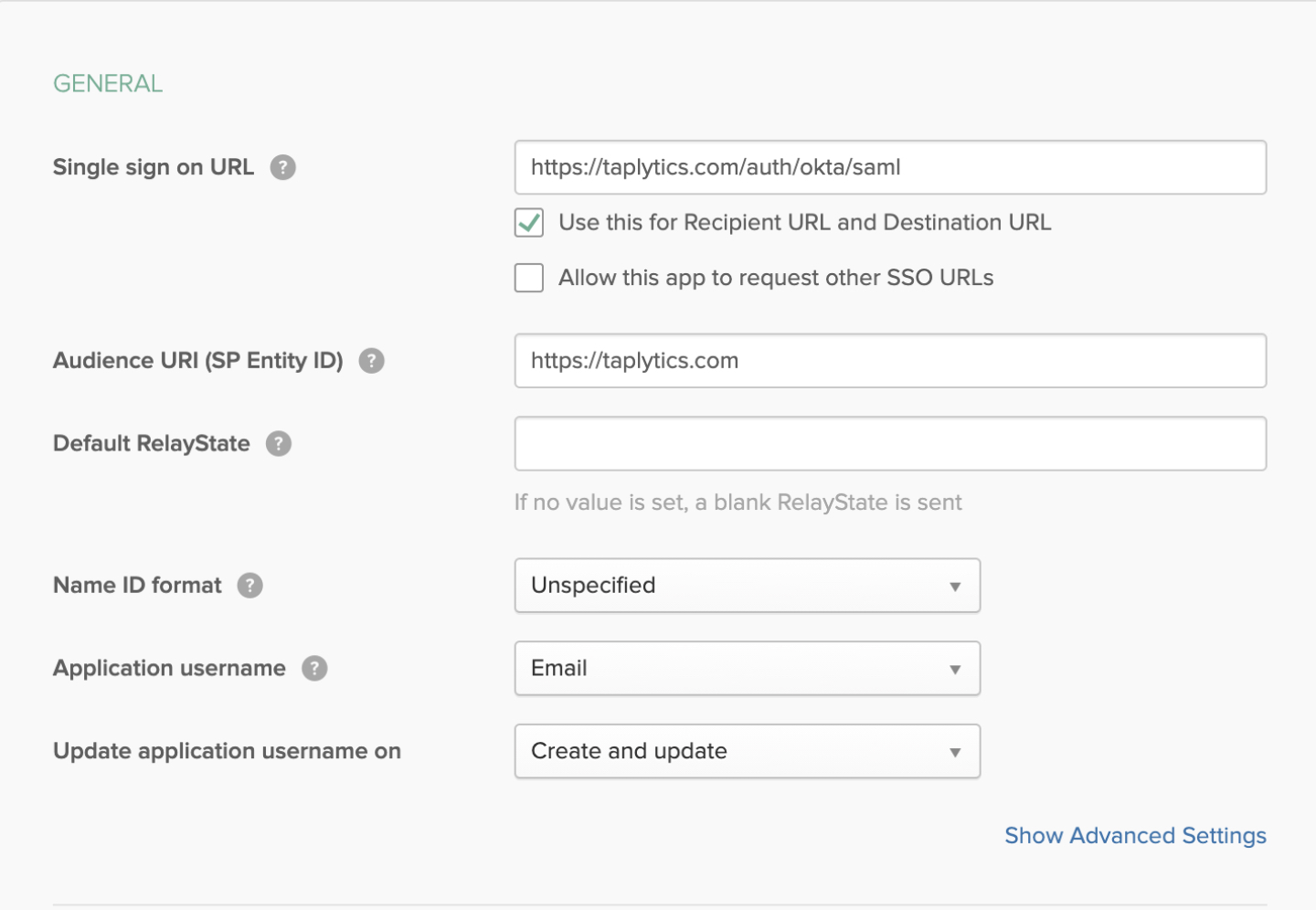
- Create a SAML SSO application on Okta for Taplytics. You will need the details below:
- Single sign-on URL: https://taplytics.com/auth/okta/saml
- Audience URI (SP Entity ID): https://taplytics.com
- Application username: Email
- All other fields can be default (see image below)
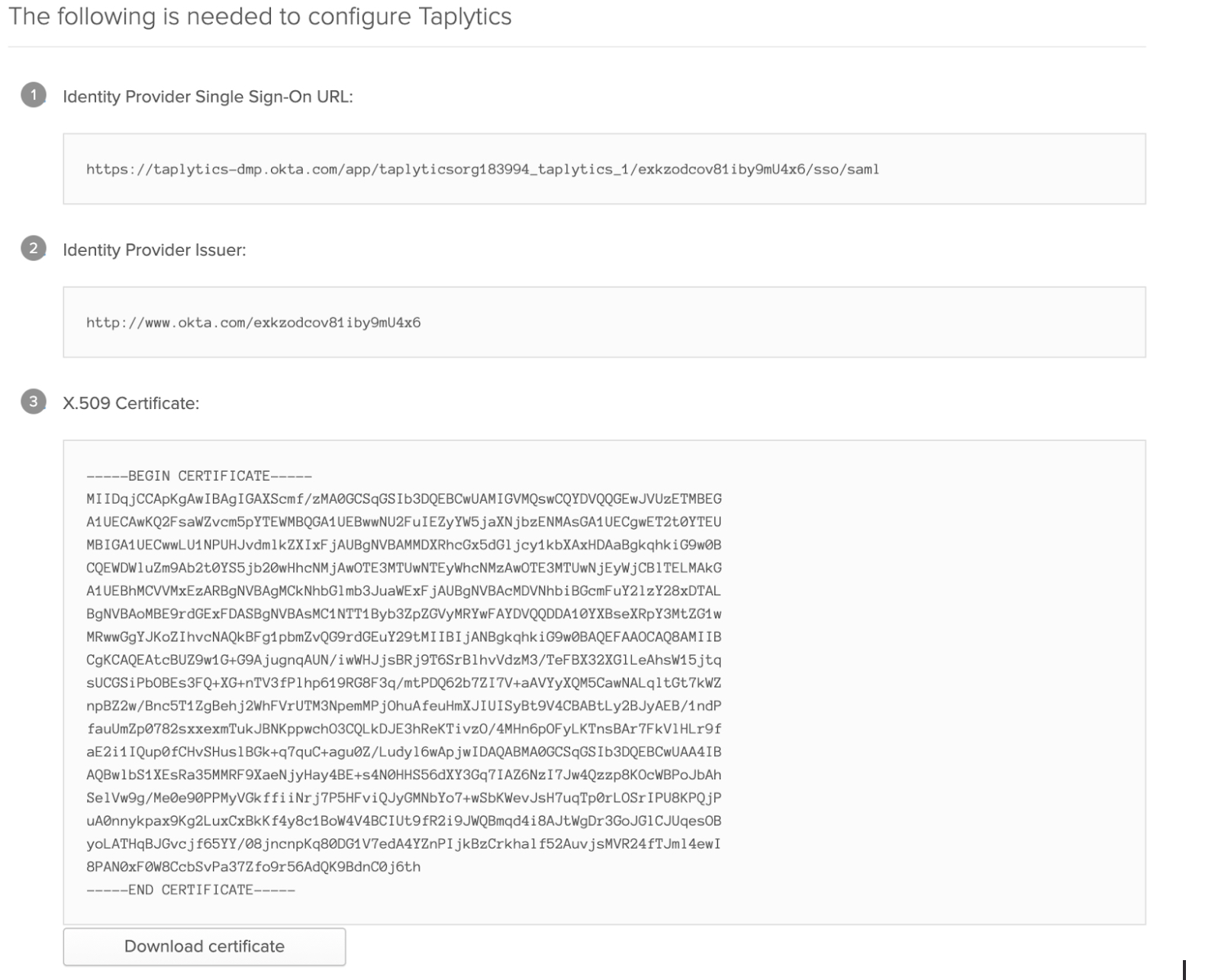
- Send Taplytics the following items:
- The Identity Provider Single Sign-On URL
- Identity Provider Issuer
- X.509 Certificate from the Okta app
The final step of any of the custom access features you decide you leverage will require you to work with your Taplytics Customer Success Manager as these details require private setup instructions for your specific environment.
Updated about 4 years ago